When to Use Sudo in Ubuntu Server
Understanding when to use the sudo command is essential for anyone managing an Ubuntu server. The sudo command grants temporary administrative privileges, allowing users to perform tasks that typically only…
Understanding when to use the sudo command is essential for anyone managing an Ubuntu server. The sudo command grants temporary administrative privileges, allowing users to perform tasks that typically only…

Learn about file hashes, their importance in cybersecurity, and how they're used for verifying file integrity, detecting malware, and more.""Understand the power…

As nations around the world expand their digital presence, they also face the growing threat of cyber warfare.
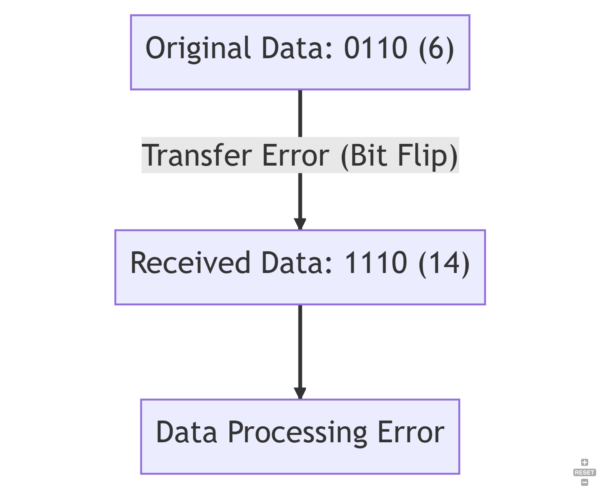
Learn about bit flips, their causes, consequences, and prevention methods in this informative article