
TikTok Privacy: Myths vs. Reality
Learn about TikTok's privacy risks & reality, why people are concerned, what personal info the app can access, & how to restrict it.

Learn about TikTok's privacy risks & reality, why people are concerned, what personal info the app can access, & how to restrict it.

As nations around the world expand their digital presence, they also face the growing threat of cyber warfare.

Learn 5 strategies to combat cybercrime and protect your organization's digital assets

PHP is a popular programming language, but its simplicity and flexibility can also be its biggest weakness.
Embracing a JavaScript-lite internet for faster, more secure, and accessible web experiences

"Cyber threats and vulnerabilities are becoming more sophisticated, making it challenging for traditional security measures to keep up.
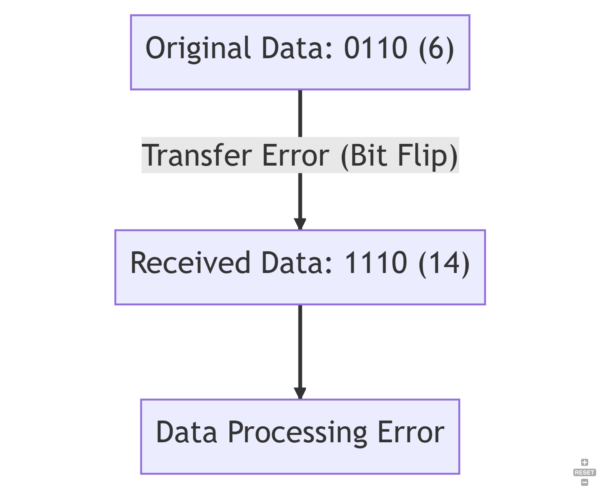
Learn about bit flips, their causes, consequences, and prevention methods in this informative article
10 Tips for Creating a REST API - Learn how to design a robust, efficient and user-friendly REST API.

Why Database Encryption Alone Is Not Sufficient for Cybersecurity" highlights the limitations of database encryption and emphasizes the importance of a comprehensive approach to cybersecurity