
TikTok Privacy: Myths vs. Reality
Learn about TikTok's privacy risks & reality, why people are concerned, what personal info the app can access, & how to restrict it.

Learn about TikTok's privacy risks & reality, why people are concerned, what personal info the app can access, & how to restrict it.
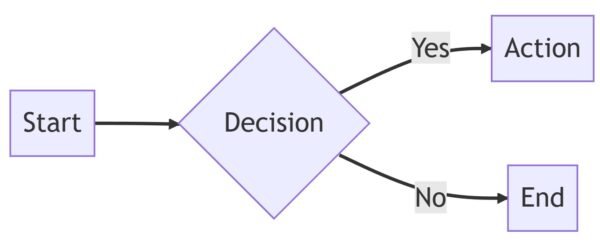
Mermaid is a powerful tool for creating and maintaining business process diagrams, providing valuable insights and improving efficiency

Learn 5 strategies to combat cybercrime and protect your organization's digital assets

Why Database Encryption Alone Is Not Sufficient for Cybersecurity" highlights the limitations of database encryption and emphasizes the importance of a comprehensive approach to cybersecurity

The Ring Doorbell 2 is a smart home security device that lets you know who comes to your front door.
Discover insights from a WordPress honeypot experiment: 676 login attempts in a month, top countries, popular login methods, and risky username/password choices.
Are WordPress developers "real" developers? This article explores the definition of a developer and whether WordPress developers fit the bill.
Are WordPress developers "real" developers? This article explores the definition of a developer and whether WordPress developers fit the bill.
10 important things to keep in mind when sending or receiving emails, including security concerns, lack of control over the email's fate, ease of forgery in the "from" field, risks…